Should I remove the Server header?
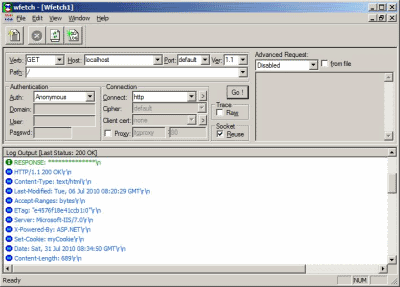
(Kristofer Gafvert, August 2, 2010)When IIS responds to a request, it does not only send the actual data, it also sends response headers. These looks something like the following:
Something that has been up for discussion many times is the Server header. Some claims that revealing the server software/version is a security risk. They say that it is possible to target an attack for that specific server.
While this may be true for some hackers (usually so-called "script kiddies" who really have no idea what they are doing), the hackers you should worry about are much more clever than this.
Since the Server header can easily be changed (not only for IIS, this applies to all the common web server software), serious hackers dont rely on it. Instead they will look at patterns and fingerprints, to figure out what server software you use. Some of the things they look at follows:
- The HTTP header field ordering (IIS sends the headers in a specific order, other web server software send them in another order).
- The response when an incorrect HTTP version is used.
- The response when an incorrect protocol is used.
- The response for a HTTP delete request.
- The response for a correct GET request for an existing resource.
- The response of a GET request of a non-existing resource.
- The response of a GET request with an URI larger than 1024 bytes.
- The response of a GET request including common attack patterns (such as %% or ../ to navigate beyond the websites folder.
- ... many more ways.
As you can see, masking the Server header is more or less useless. A serious hacker looks at other things to figure out what web server software you use.
In conclusion; Change the Server header if you want to. But do not do this with the purpose of making the server more secure, because that is not true. It only gives you a fake feeling of being more secure.
The key is to configure the server properly and keep it updated against bugs (especially security bugs). If you do that, you will not run into any problems. In my opinion it is a waste of time to try to mask or hide that you are running IIS. If someone wants to find out that you are running IIS, they will for sure do it somehow. And if they fail this, and you are the target of an attack, they will attack you any way in one or another way.
For IIS 6.0, 7.0 and 7.5, you can use URLScan to remove the Server header by setting RemoveServerHeader to 1.
Applies to [?]
IIS 6.0, IIS 7.0, IIS 7.5